- Home
- Learn
- Healthcare
- What is HIPAA Compliance? A Complete Guide for 2026
HEALTHCARE
What is HIPAA Compliance? A Complete Guide for 2026
Contents
What happens to a patient’s health information once they share it with their doctor or, say, their pharmacist?
For the most part, they may not care. They assume it’s safe and out of reach for prying eyes. But behind the scenes, there’s a framework that makes this trust possible.
A set of rules that ensures accountability when sensitive healthcare data is mishandled. With consequences that hit hard, they leave no room for carelessness.
These rules that stand guard over important patient information are termed HIPAA.
For healthcare organizations, HIPAA is not just a set of agreements one can skim through like a terms-and-conditions pop-up before clicking “I agree.” Without consistent actions, the pact can easily be broken, which might lead to dire consequences.
So, whether you’re a small clinic, a global healthcare provider, or even a tech vendor in the healthcare domain, understanding HIPAA is essential.
In this guide, we’ll cut through the legalese and get to the heart of HIPAA: who it applies to and how it impacts the way healthcare operates in today’s digital-first world.
But to really appreciate why HIPAA compliance matters, we need to first rewind the clock to a time when healthcare was just beginning to evolve — a time when privacy wasn’t always a given.
Back in 1996, the healthcare world was at a crossroads. The digital revolution was beginning to reshape industries, and healthcare was no exception. Patient records, once locked away in file cabinets, were starting to move online. It was efficient, yes — but it also raised questions no one had to ask before: How do we keep this sensitive information safe? Who gets to see it, and who doesn’t?
That’s where HIPAA—the Health Insurance Portability and Accountability Act—came into being.
Signed into law by President Bill Clinton, the original purpose of HIPAA wasn’t just to protect privacy, but to make healthcare more efficient, fair, and accessible. It tackled challenges like ensuring continuity of coverage for employees switching jobs, protecting individuals with pre-existing conditions, and addressing “job lock”, a situation where people felt trapped in their jobs for fear of losing health insurance. It also sought to simplify the industry’s growing reliance on electronic transactions.
However, as electronic health records became the norm, the potential risks became clearer. Medical data flowing through networks and across borders meant protecting patient privacy was a matter of urgency.
So, HIPAA added a new layer of safeguards: national standards to shield Protected Health Information (PHI) from misuse or unauthorized access.
Over the years, these regulations have evolved (and continue to do so) to address new challenges in an ever-changing digital landscape.
But what exactly constitutes the information that these rules strive to protect?
This brings us to a term we just touched on: Protected Health Information, or PHI — which is the key element of everything HIPAA is built to safeguard.
Healthcare is often a deeply personal matter. For many, sharing their health conditions with even close family or friends can feel uncomfortable. There’s something about laying bare our vulnerabilities that makes us hesitate. Given that, how many of us would want someone outside our close personal circle to know about our diagnosis, treatment plans, or long-term conditions?
This rightful sense of hesitation, of wanting to keep something so personal under wraps, is what makes Protected Health Information (PHI) so relevant.
At its core, PHI covers any piece of information that links you to your health status. If someone could use some detail to identify you and learn about your medical history, treatments, or billing, it falls under the protection of HIPAA.
This could be:
Whether it’s shared through an email, on paper, or spoken aloud, PHI is protected by rules that ensure it’s only accessed by the right people, for the right reasons.
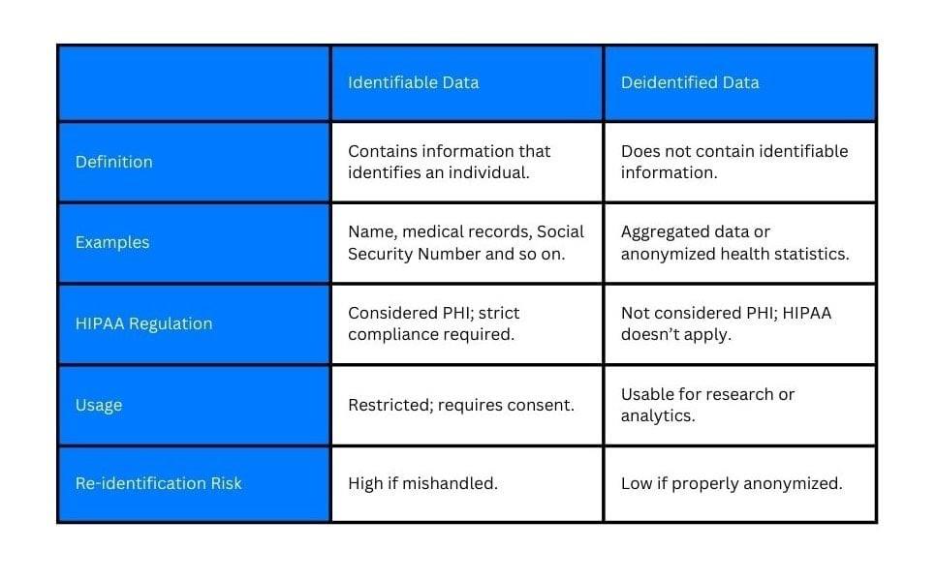
Not all information is created equal. Some are prioritized for protection over others.
Firstly, we have unique identifiers. This includes your name, your diagnosis, your contact details, and so on. These are the pieces that make up what we call “identifiable data.” This is the kind of information that could easily be traced back to you, which is why it’s protected under HIPAA.
But not all health data needs to stay tied to a person. Sometimes the information can be stripped of the personal markers that link to an individual. This is called de-identified data.
Though still relevant, these data no longer fall under the same tight protections of HIPAA.
If you are having trouble imagining how de-identified data would look like, here are some examples:
De-identification of PHI allows healthcare providers to share valuable data for research or analysis while still respecting individuals’ privacy. Removing identifiers ensures that even if data is exposed, it can’t be tied back to an individual.
We’ve seen what Protected Health Information is and why it matters. Now, let’s look at the pillar rules of HIPAA that exist to protect it.
You may have figured out already that HIPAA isn’t just one sweeping law. It’s a collection of carefully constructed rules designed to address specific challenges in healthcare data privacy and security.
Let’s see what they are.
The HIPAA Privacy Rule sets the boundaries for how Protected Health Information (PHI) is used and disclosed. Under 45 CFR § 160.103, PHI includes individually identifiable health information in any form—whether verbal, electronic, or written—that can be linked to a specific individual.
Beyond restricting access, the rule also gives patients control over their data. Individuals have the right to access their health records (45 CFR § 164.524), request corrections (45 CFR § 164.526), and understand how their information is used. It also enforces the “minimum necessary” standard under 45 CFR § 164.502, ensuring that only the least amount of information required is disclosed.
The Privacy Rule applies to both of the following groups (45 CFR § 160.102):
These include healthcare providers, health plans, and clearinghouses that directly handle patient information.
These are third-party service providers—such as IT vendors, cloud storage companies, or billing firms—that handle PHI on behalf of covered entities, as defined under 45 CFR § 164.504(e).
If the Privacy Rule is about control, the HIPAA Security Rule is about protection. This rule focuses on safeguarding electronic Protected Health Information (ePHI) through a structured set of safeguards.
Healthcare organizations must implement measures across three key areas:
Policies, procedures, and workforce training designed to manage security risks. This includes conducting risk analyses, implementing risk management practices, and responding to security incidents.
Controls that protect physical access to systems and facilities, such as secure server locations and restricted access to equipment handling ePHI.
Technologies like access controls, audit logs, and encryption to ensure only authorized users can access ePHI and that data remains secure during storage and transmission.
Regulators are also increasingly emphasizing stronger cybersecurity practices, including more rigorous risk analysis and improved incident response, reflecting the growing threat of data breaches and ransomware.
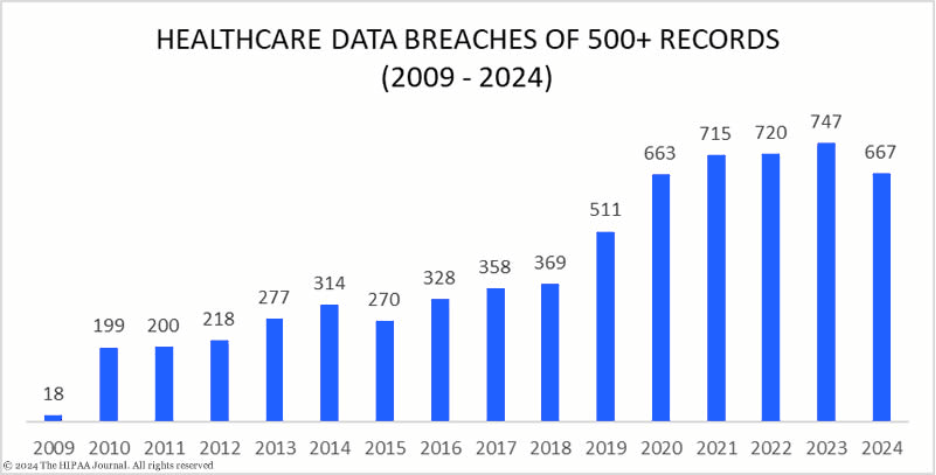
Mistakes happen, and when they do, the HIPAA Breach Notification Rule ensures transparency. If a breach occurs, covered entities are required to inform impacted individuals, report the incident to the Department of Health and Human Services (HHS), and, when applicable, notify the media.
Also, timelines matter. Under 45 CFR § 164.404, organizations must notify affected individuals without unreasonable delay and no later than 60 days after discovering a breach. This ensures patients can take timely steps to protect themselves.
Scale determines reporting requirements. If a breach affects 500 or more individuals in a single state or jurisdiction, organizations must notify prominent media outlets within the same 60-day window (45 CFR § 164.406).
Organizations must also report breaches to HHS (45 CFR § 164.408). For incidents involving 500 or more individuals, notification must be completed within 60 days. Breaches affecting fewer individuals may be compiled and reported once a year.
This rule acts as an accountability checkpoint, ensuring organizations take responsibility and keep patients informed when their data may have been compromised.
Rules without consequences are just suggestions, and HIPAA doesn’t deal with suggestions. The HIPAA Enforcement Rule is where accountability becomes non-negotiable.
Defined under 45 CFR Part 160, Subparts C–E, this rule outlines how compliance is monitored and enforced. It empowers the Department of Health and Human Services (HHS) to investigate complaints (45 CFR § 160.306), conduct compliance reviews (45 CFR § 160.308), and impose civil monetary penalties (45 CFR § 160.404) when violations occur.
Penalties can range from monetary fines to corrective action plans, and in severe cases, violations may also lead to criminal charges under federal law.
The HHS Office for Civil Rights (OCR) has also increased its focus on proactive enforcement through risk-based audits and investigations, particularly around cybersecurity compliance. Organizations are now expected not just to implement safeguards, but to demonstrate ongoing risk management and accountability.
Recent updates aligning 42 CFR Part 2 with HIPAA have also expanded enforcement expectations for organizations handling sensitive substance use disorder data.
The Omnibus Rule broadly reinforces and extends HIPAA requirements. Finalized in 2013, it updates multiple parts of the HIPAA regulations to address evolving risks in healthcare data management.
One of its most significant changes is extending direct liability to business associates — including contractors, vendors, and third-party service providers. Under 45 CFR § 160.402(c), these entities are held accountable for compliance, not just the covered entities they work with.
The rule also reinforces the need for formal agreements governing data handling. Business Associate Agreements (BAAs), defined under 45 CFR § 164.504(e), must clearly outline responsibilities for safeguarding Protected Health Information (PHI).
Together, these rules leave no room for ambiguity.
But the question remains: who all falls under HIPAA’s watchful eye?

When we talk about HIPAA compliance, most people think of the obvious players: hospitals, clinics, and insurance providers – the ones directly interacting with patients. But the web of responsibility is much wider.
At the forefront are the covered entities (healthcare providers, insurers, pharmacies) organizations that deal with protected health information as part of their core operations. Their role is clear, and so is their accountability.
Then there are the business associates. They include the tech platforms managing patient records, insurance companies processing claims, billing services handling payment information, and more. Business associates work on behalf of covered entities like hospitals or clinics, often using PHI.
In short, if you handle patient data in the healthcare industry, directly or indirectly, you’re part of the chain of trust.
What happens when you violate HIPAA regulations? Before we look at the penalties, let’s understand the most common mistakes that lead to them.
Sharing PHI without proper authorization, even accidentally.
Failing to implement appropriate security measures to protect sensitive data.
Employees not being trained to handle PHI correctly or identify potential risks.
Not informing patients or authorities within the required timeframe.
| Tier | Violation Type | Description | Minimum Penalty (Per Violation) | Maximum Penalty (Per Violation) | Annual Cap |
| Tier 1 | Unknowing | The organization was unaware of the violation and could not have reasonably avoided it | $145 | $73,011 | $2,190,294 |
| Tier 2 | Reasonable Cause | The violation occurred due to reasonable cause, not willful neglect | $1,461 | $73,011 | $2,190,294 |
| Tier 3 | Willful Neglect (Corrected) | Violation due to willful neglect, but corrected within the required timeframe | $14,602 | $73,011 | $2,190,294 |
| Tier 4 | Willful Neglect (Uncorrected) | Violation due to willful neglect and not corrected | $73,011 | $2,190,294 | $2,190,294 |
The financial consequences of HIPAA violations are significant and are adjusted annually for inflation. The latest update, published in the Federal Register on January 28, 2026, revised penalty amounts to maintain their deterrent effect.
Under 45 CFR § 160.404, the Office for Civil Rights (OCR) enforces a four-tier penalty structure based on the severity of the violation:
Minimum $145 per violation, up to $73,011 per violation, with an annual cap of $2,190,294
Minimum $1,461 per violation, up to $73,011 per violation, with an annual cap of $2,190,294
Minimum $14,602 per violation, up to $73,011 per violation, with an annual cap of $2,190,294
Minimum $73,011 per violation, up to $2,190,294 per violation, with an annual cap of $2,190,294
These amounts apply to penalties assessed on or after January 28, 2026.
In addition to civil penalties, HIPAA violations can also result in criminal charges under federal law, particularly in cases involving intentional misuse of PHI. Penalties may include:
Beyond legal and financial consequences, HIPAA violations can cause long-term damage to an organization’s reputation. Loss of patient trust, strained partnerships, and negative publicity can significantly impact business operations and growth.
One of the most cited HIPAA enforcement cases involved Children’s Medical Center of Dallas, which was fined $3.2 million by the Office for Civil Rights (OCR), a division of the U.S. Department of Health and Human Services (HHS), for multiple violations spanning several years.
The case began after the loss of an unencrypted, non-password-protected BlackBerry device containing the electronic protected health information (ePHI) of approximately 3,800 patients. Additional incidents followed, including the theft of an unencrypted laptop affecting over 2,400 individuals.
What made this case particularly serious was not just the breaches themselves, but the organization’s failure to act on known risks. Security assessments conducted as early as 2007 had already recommended encryption and stronger safeguards, yet these measures were not implemented for years.
OCR found that the organization lacked adequate risk management processes and continued using unsecured devices despite repeated warnings. Encryption of devices was only fully implemented in 2013—years after the initial risks were identified.
This case highlights a critical lesson: HIPAA violations are not only caused by a single mistake, but by repeated failure to address known vulnerabilities.
Healthcare marketing operates under strict privacy rules, especially when patient information is involved. Under HIPAA, marketing is not prohibited—but it is tightly regulated, particularly when it involves Protected Health Information (PHI).
HIPAA defines marketing and sets boundaries on when patient authorization is required. In general, any communication that promotes a product or service and uses identifiable PHI requires prior patient authorization (45 CFR § 164.508).
However, not all outreach is considered “marketing.” Communications related to treatment, care coordination, or general health education may be permitted without authorization under (45 CFR § 164.501).
Marketing includes:
These activities require explicit, written patient authorization.
You can communicate without authorization when:
The key distinction is whether the message is promotional vs care-related.
Do not include identifiable patient information in marketing materials unless you have explicit authorization. Instead:
Even de-identified data must meet HIPAA standards (45 CFR § 164.514).
If your campaign involves PHI:
Authorization requirements are defined under (45 CFR § 164.508).
If you receive financial compensation for promoting a product or service:
This is a common compliance gap within partnerships and co-marketing campaigns.
Patient stories are powerful, but also risky:
Adopt a “minimum necessary” approach:
Marketing teams often rely on digital channels—but not all tools are HIPAA compliant.
Any email or message containing PHI must be secured using appropriate safeguards, including encryption where applicable (45 CFR § 164.312(e)).
Standard email and SMS are not inherently HIPAA-compliant. Using them without safeguards can expose PHI to unauthorized access.
Handling sensitive patient data manually or relying on outdated methods isn’t just inefficient; it’s risky. Paper-based records can be misplaced, human errors in data entry can lead to breaches, and monitoring who accessed what information can become a logistical nightmare.
Technology becomes indispensable here:
Tech minimizes the errors that are common in manual processes. Automated systems ensure data is entered and stored consistently and accurately.
As healthcare organizations grow, managing more data becomes complex. Technology scales with the organization, ensuring compliance measures remain robust.
Technology allows for real-time monitoring, audit trails, and automated reports that make compliance tracking straightforward and transparent.
Digital tools encrypt sensitive data, secure it during transmission, and allow only authorized access — things that are hard to achieve with physical files or outdated software.
Advanced systems detect potential vulnerabilities or breaches before they become critical issues, something that isn’t possible with manual oversight.
Here’s a list of popular tools used in healthcare that involve data handling.
Healthcare has always been about more than just treatments. It’s also about relationships; with patients, providers, and everyone in between. But as the industry becomes increasingly complex, maintaining those relationships and keeping track of sensitive data becomes a challenge.
That’s where Healthcare CRMs come in.
While they’re not as foundational as EHR systems, healthcare CRMs have carved out a vital role in the healthcare tech ecosystem by focusing on the patient management, relationship, and communications sides of care, all while ensuring HIPAA compliance.
Here’s what CRMs can do to ensure HIPAA compliance and how providers can best use the tool within the bounds of HIPAA.
A core requirement of HIPAA is protecting electronic Protected Health Information (ePHI) through appropriate safeguards. Healthcare CRMs support this by embedding security into everyday operations.
Data is protected both in transit and at rest, reducing the risk of unauthorized access during storage or transmission.
Access to patient data is restricted based on user roles, ensuring individuals only see the information necessary for their responsibilities.
User activity is logged to help monitor access and support investigations or compliance reviews.
Automated backups and recovery systems help ensure data remains available and protected in case of system failures.
HIPAA compliance applies to how patient data is shared. CRMs help standardize and secure communication across channels.
Built-in protections help ensure that communication containing sensitive data remains protected.
Patients can securely access records, schedule appointments, and communicate with providers in a controlled environment.
Integrated tools enable secure virtual consultations while maintaining compliance requirements.
CRMs that integrate with clinical systems help maintain consistency in how patient data is handled across platforms.
Data flows between systems with reduced manual entry, lowering the risk of errors and exposure.
Patient interactions and records are accessible in one place while maintaining consistency across systems.
Organizations can monitor how data is accessed and used, supporting audit readiness and accountability.
HIPAA compliance requires continuous monitoring and proper documentation. CRMs help operationalize these processes.
Communication history and patient interactions are automatically documented for compliance purposes.
Systems maintain records that can support internal reviews and regulatory audits.
Standardized processes ensure that teams follow approved procedures when handling patient data.
A well-implemented healthcare CRM allows organizations to streamline operations while maintaining strict privacy controls.
Patient information from multiple systems is brought into one place for easier, controlled access.
Routine tasks such as reminders and follow-ups can be automate and handled efficiently within secure systems.
Analytics help organizations improve engagement and performance without exposing unnecessary data.
Simplified processes allow teams to focus more on patient care while maintaining compliance.
Building an effective HIPAA compliance program means creating a structured, ongoing system of policies, processes, and safeguards to ensure your organization consistently meets regulatory requirements. It’s not a one-time effort, but a continuous process that evolves with changing risks and regulations.
Develop clear, written policies covering privacy, security, and breach notification requirements. Ensure they are regularly reviewed and updated to reflect regulatory changes, evolving threats, and operational changes within your organization.
Designate a privacy officer and a security officer responsible for overseeing compliance efforts. These roles should manage policy implementation, handle incidents, and ensure the organization stays aligned with HIPAA requirements.
Conduct regular, organization-wide risk assessments to identify vulnerabilities across systems, processes, and workforce practices. Move beyond periodic reviews by adopting a proactive risk management approach that addresses emerging threats such as ransomware and insider risks.
Provide role-based HIPAA training tailored to employees’ responsibilities. Go beyond initial onboarding by offering continuous education, including updates on emerging threats, phishing awareness, and secure data handling practices.
Adopt strong access controls, encryption, and multi-factor authentication where appropriate, as these are increasingly expected under evolving regulatory guidance. Ensure systems are regularly updated, monitored, and backed up, with clear incident response and disaster recovery plans in place.
Use HIPAA-compliant tools for transmitting PHI, including email, messaging, and telehealth platforms. Ensure appropriate safeguards such as encryption are in place and that patient consent requirements are followed where applicable.
Encourage employees to report potential issues or violations without fear of retaliation. Establish clear reporting channels and ensure concerns are reviewed and addressed promptly to reduce risk.
Maintain detailed records of compliance activities, including training, risk assessments, incident responses, and audits. Conduct regular internal audits to identify gaps and demonstrate compliance during regulatory reviews.
Ensure all business associates sign and comply with updated Business Associate Agreements (BAAs). Regularly assess vendor security practices, as third-party relationships remain a significant source of HIPAA risk.
Apply consistent disciplinary measures for non-compliance. In the event of a breach, act quickly to contain the issue, investigate the root cause, meet notification obligations, and implement corrective actions to prevent recurrence.
Monitor regulatory updates and enforcement trends, including proposed changes to the HIPAA Security Rule and increasing focus on cybersecurity. Adapting proactively helps reduce compliance risk and avoid penalties.
Maintain audit-ready documentation and regularly test your compliance program. Organizations should be able to demonstrate adherence to HIPAA requirements at any time, as regulatory audits and investigations can occur without prior notice.
Use this checklist to assess your organization’s HIPAA compliance. Each item is aligned with specific regulatory requirements and includes practical steps you can evaluate and document during an internal audit.
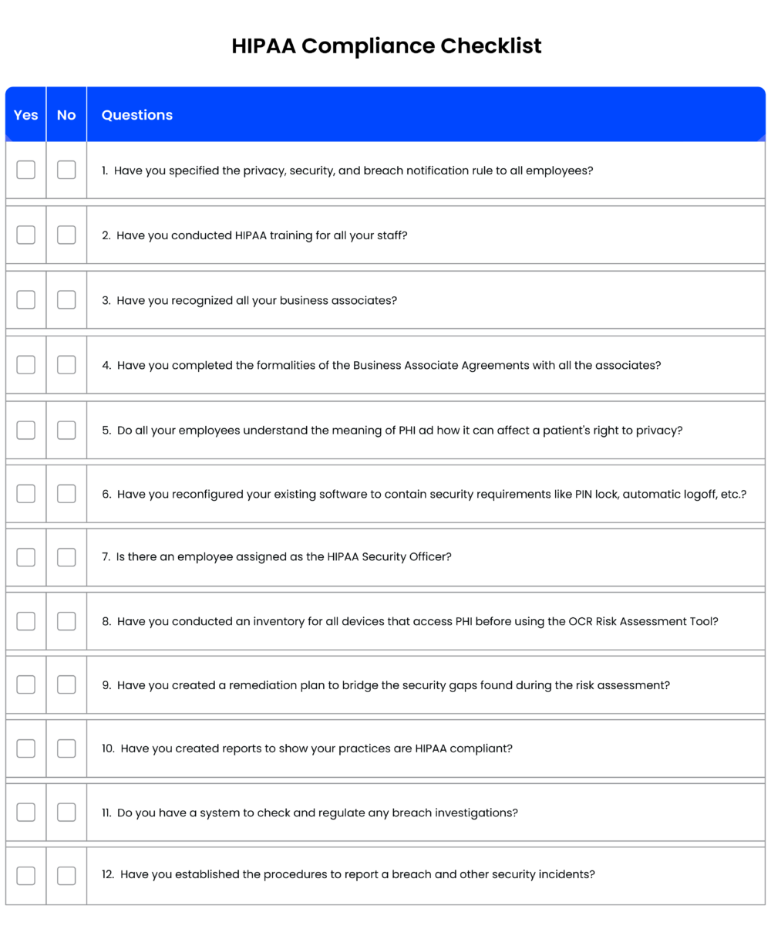
[You can also download the checklist to share it with your team: 12 Rule HIPAA Compliant Checklist]

If you’re looking for a HIPAA-compliant solution to manage your healthcare practice’s operations and more, a healthcare CRM might be the answer.
An end-to-end patient relationship management platform/healthcare CRM such as LeadSquared, can assist in creating a secure, single-source overview for patient profiles, health histories, appointment schedules, and more.
Additionally, integrating an EHR system within our HIPAA-compliant CRM ensures that providers can manage and access personal health information (PHI) securely. Certified EHR systems allow individuals to request their health information in electronic forms, adhering to privacy regulations.
It can also help facilitate your other significant needs:
And with a system like LeadSquared, a HIPAA Business Associate Agreement always comes standard.
Get in touch with our team to know more!
Anyone in the healthcare industry handling PHI. This includes doctors, hospitals, insurance companies, and even third-party vendors like billing services or IT providers. If a business interacts with patient data in any way, they likely need to follow HIPAA’s rules. Even healthcare CRMs must have safeguards in place to ensure compliance.
Individually Identifiable Health Information (IIHI) is any health data linked to a specific person, like name, birth date, or medical history. PHI is IIHI that is created, stored, or shared by a HIPAA-covered entity (like a doctor or insurer) in connection with healthcare services. PHI is legally protected, while IIHI outside the healthcare system (like in a personal health app) isn’t.
HIPAA classifies healthcare clearinghouses as covered entities, meaning they must follow strict privacy and security rules when handling PHI. Since clearinghouses process medical claims and billing data between providers and insurers, they must encrypt data, control access, and ensure secure transmission.
HIPAA ensures health insurance portability by allowing employees to maintain coverage when switching jobs. It prevents exclusions based on pre-existing conditions and reduces coverage gaps, making healthcare more accessible.
No, HIPAA generally does not apply to employers in their role as employers. It applies to healthcare providers, health plans, and their business associates.
However, if an employer operates a self-insured health plan, that specific function may be subject to HIPAA rules. This is a common misconception—many people assume all health-related data is automatically protected under HIPA
Yes. HIPAA applies to all covered entities, regardless of size, as long as they handle PHI and conduct standard electronic transactions.
Even small clinics, dental practices, or solo providers must implement safeguards, train staff, and maintain compliance programs.
HIPAA itself does not provide a private right of action, meaning patients cannot directly sue under HIPAA law.
However, patients can:
File complaints with regulators (like OCR)
Pursue lawsuits under state laws (e.g., negligence, breach of privacy)
This distinction is often misunderstood but important for both providers and patients.
The “minimum necessary” rule requires organizations to limit the use, disclosure, and access to PHI to only what is needed for a specific purpose.
For example:
A billing team should only access billing-related data
Marketing teams should not access full medical records
This principle reduces risk and is a core part of HIPAA compliance.
Enter your details and we'll send you a quick confirmation email to verify your address.